Atlantic-IT : Blog
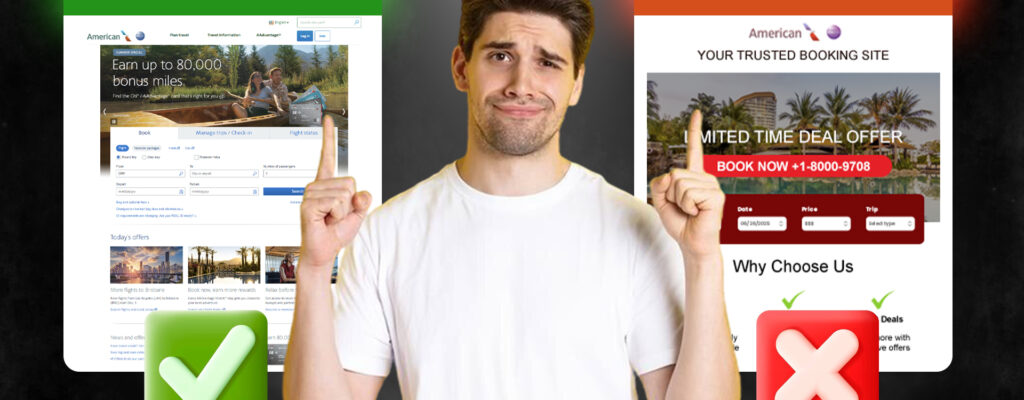
The One Click That Could Ruin Your Vacation
Just because summer is winding down doesn’t mean the travel risks are. Whether you’re squeezing in one last vacation or planning a Labor Day escape, it’s good to stay alert. Cybercriminals are always looking for ways to exploit unsuspecting travelers,…
Read More about The One Click That Could Ruin Your VacationData Shakedown
Ransomware attacks becoming more frequent and more sophisticated, and aimed at manufacturing companies. Security researchers and law enforcement officials say the spread of ransomware attacks has reached epidemic proportions, with organizations of all sizes in both the public and private…
Read More about Data ShakedownRelieving Password Headaches
Atlantic-IT.net provides tools and techniques for making passwords easier to manage while improving security. Last Friday, the accounting system required Dave to change his password since it had been more than 90 days since his last reset. Dave was rushed,…
Read More about Relieving Password HeadachesSmart MFPs
Latest multifunction devices enhance workflow automation with app integration and programmability. Businesses have pursued the promise of the “paperless office” for the past 40 years, but the reality is that companies of all sizes still rely heavily on printed materials.…
Read More about Smart MFPsBetter Backup for Manufacturers
Cloud and virtualization-specific backup options help overcome the limitations of traditional solutions in manufacturing companies. Data backup is arguably the most critical function in IT, but it continues to be a frustrating and problematic process for most organizations. Manufacturing companies…
Read More about Better Backup for ManufacturersTechnology Horizons – Vol. 12 # 1
While businesses need to manage expenses, a lower-cost solution isn’t always the best value. That’s particularly true when it comes to IT support. Cedar Hill Golf and Country Club decided to change IT providers based upon price, but returned to…
Read More about Technology Horizons – Vol. 12 # 1Sticking with the Best
Cedar Hill Golf and Country Club decides to try another outsourced IT provider — and quickly returns to Atlantic-IT.net. Here’s why. “The grass is always greener on the other side of the fence.” It’s an old proverb that neatly sums…
Read More about Sticking with the BestThe Art of Network Security
Security assessments can help organizations win the war against cyberattacks by identifying and remediating vulnerabilities. “If you know your enemies and know yourself, you can win a hundred battles without a single loss.” –Sun Tzu, The Art of War Sometime…
Read More about The Art of Network SecurityRecent Posts
Atlantic-IT.net is the perfect IT company to support all your technology needs.
Schedule your initial consultation with our team of IT professionals by filling out the form below.
"*" indicates required fields
Categories
Categories
- Backup
- Blog
- Budgeting
- Business Continuity
- Business Continuity
- Case Studies
- Cloud
- Desktop Virtualization
- Desktop-as-a-Service
- Disaster Recovery
- HIPAA Compliance
- Infographic
- IT Support
- Managed Services
- Mobility
- News
- Newsletter
- Newsletters
- Outsourced IT
- Outsourced IT
- PCI Compliance
- Phishing Simulation
- Security
- SMB Strategy
- Storage
- Uncategorized
- Unified Communications
- vertical market news
- Virtualization
- VoIP